With billions of people actively engaging on social media, it’s no secret that content creation is a key factor in any digital marketing strategy. But let’s face it, not everyone excels at it. Some posts capture attention effortlessly—funny, engaging, or informative—while others fall flat.
Thankfully, that’s not you. You’re someone who keeps up with the latest trends in digital marketing. You understand that building a brand, captivating an audience, and standing out in the crowded social space requires more than just luck—it demands a solid strategy.
Content is the heart of every social media plan. It’s the first impression your brand makes and the lasting connection it forms with customers. That’s why understanding what type of content to post on each platform is essential for success. In this guide, we’ll explore key strategies, tools, and trends that are helping brands strike the right chord with audiences.
Most Engaging Social Media Content Marketing Strategies For Your Business
In today’s fast-paced digital world, keeping up with the ever-evolving landscape of social media platforms, features, and algorithms can feel overwhelming. Based on data from 729,000 public social profiles collected in 2022, Sprout Social analyzed trends to determine the types of content that inspire the most interaction.
Below, let’s explore which formats are driving engagement and how you can incorporate them into your social strategy.
Short-form video
Source: Influencer Marketing Hub
Short-form videos are one of the most engaging forms of social media content. Their ability to present information in less than one minute makes them easily digestible and highly shareable, which is crucial in today’s fast-paced digital landscape.
Audiences are looking for immediate entertainment, which is why a concise video often outperforms longer content. Short-form videos don’t require extensive resources or heavy editing to be effective—authenticity and relatability are often enough to captivate an audience. Let’s explore why short-form video works and the best platforms to leverage it.
| Reason Why Short-Form Video Works | Best Platforms |
|---|---|
| 66% of consumers find short-form videos the most engaging type of content on social media. | TikTok: Offers creative tools like filters and music for short videos. |
| Short-form videos are 2.5x more engaging than long-form videos. | Instagram Reels: Includes a variety of tools for creating free videos, plus native ads. |
| Consumers crave authentic, non-promotional content from brands. | YouTube Shorts: With 15 billion global daily views, it’s a rapidly growing platform for short videos. |
| Versatile for product demos, influencer collaborations, and behind-the-scenes content. |
Long-Form Video
Source: Lumen5
Long-form videos are ideal for delivering educational and comprehensive content. Unlike short-form videos, which offer quick bites of information, long-form videos provide depth and authority on various subjects.
Why Long-Form Video Works on Social Media
- In-Depth Engagement: 24% of consumers find long-form videos the most engaging type of content. They are effective for building relationships and delivering detailed information.
- Educational Value: 93% of viewers use YouTube for educational purposes, with an average viewing time of nearly 30 minutes per session.
Best Social Media Platforms for Long-Form Video
| Platform | Advantages for Long-Form Content |
|---|---|
| YouTube | Ideal for sharing and discovering long videos; designed for extended viewing. |
| Popular for live videos and lengthy posts; supports long video uploads. |
Live Video

Source: Restream
With the rise of digital transformation, live video has become a powerful tool for real-time customer engagement. During the pandemic, live video saw a significant surge, with viewers reaching 152.5 million in 2020, marking a 20.4% increase from 2019.
Why Live Video Works on Social Media
- Real-Time Interaction: 37% of consumers find live video the most engaging type of social media content. It allows for immediate reactions and interactions during live events.
- Sense of Community: Live video fosters a feeling of togetherness and real-time connection with the audience.
- Content Repurposing: Livestreams can be repurposed into shorter clips or text snippets for use on other platforms, maximizing content value.
Best Social Media Platforms for Live Video
| Platform | Advantages |
|---|---|
| Facebook Live | Popular for entertainment and wide reach. Allows for real-time engagement with a broad audience. |
| Instagram Live | Content appears at the beginning of Instagram stories, increasing visibility and chances of viewer engagement. |
| YouTube Live | Effective for entertainment and reaching a large audience. Suitable for diverse types of live content. |
| LinkedIn Live | Ideal for professional networking and reaching business audiences. LinkedIn Live videos receive 7x more reactions compared to native videos. |
Key Tips for Using Live Video
- Engage in Real-Time: Use live video to host interactive events like Q&As, webinars, or virtual meetings to connect with your audience in the moment.
- Promote Beforehand: Let your audience know in advance when you’ll be going live to ensure higher attendance.
- Repurpose Content: After the live session, create additional content from the livestream to share across different platforms.
Images

Source: MediaOne
Images rank as the second most valuable type of social media content. They are incredibly prevalent across various platforms due to their ability to convey messages quickly and effectively. With their immediate visual impact, images allow users to grasp brand impressions at a glance.
Why Images Work on Social Media
- Engagement: 61% of consumers find images the most engaging type of in-feed social content.
- Instant Appeal: Images can be processed and appreciated almost instantly, often requiring less effort than reading text.
- Accessibility: High-definition mobile cameras and free editing tools make it easy for anyone to create compelling images.
Best Social Media Platforms for Images
| Platform | Advantages |
|---|---|
| Originally image-centric; 87% of its content is images. Offers filters, effects, and editing tools. | |
| Ideal for inspiration and creativity; 97% of searches are unbranded. Perfect for discovery and sparking interest. Social commerce features allow for tagging products, making images “shoppable.” |
How to Leverage Images Effectively
- Instagram: Utilize the platform’s extensive suite of editing tools and filters to create visually appealing content that stands out in users’ feeds.
- Pinterest: Focus on high-quality, inspirational visuals that align with user search intent. Use social commerce features to link images directly to your products.
GIFs and Memes

Source: Agency Analytics
GIFs and memes are popular forms of social media content, especially favored by younger audiences. They effectively convey emotions and humor that words alone might struggle to capture, offering a relatable and often comedic perspective on everyday life.
Why GIFs and Memes Work on Social Media
- High Shareability: 71% of consumers expect personalized content from brands, and GIFs and memes often fit this expectation, encouraging interactions and shares.
- Relatability: These formats resonate with audiences by addressing common experiences in a humorous way, which can enhance brand relatability and engagement.
- Dynamic Content: GIFs, being animated, add a dynamic element that can drive conversations and make content more memorable.
Best Social Media Platforms for GIFs and Memes
| Platform | Advantages for GIFs | Advantages for Memes |
|---|---|---|
| Posts GIFs as short videos; great for visual engagement. | Highly effective; users share over one million memes daily. | |
| Features for sharing GIFs and creating your own using the Boomerang feature. | Memes drive high engagement and traffic to websites. | |
| Easy access to a wide selection of GIFs via the “GIF” icon. | Memes are shareable and can go viral quickly. | |
| Allows GIFs and memes; useful for professional but light-hearted content. | Memes can help in professional settings with appropriate content. |
Key Tips for Using GIFs and Memes
- Know Your Audience: Tailor your GIFs and memes to match the preferences and humor of your target demographic.
- Stay Relevant: Use trending memes and GIFs to ensure your content is timely and resonates with current conversations.
- Monitor Engagement: Track how your audience interacts with GIFs and memes to refine your content strategy and improve engagement.
Text-Based Posts

Source: Reddit
While visual content is often prioritized, text-based posts still hold significant value. They offer a direct way to convey your brand’s personality and engage with your audience through meaningful conversations.
Why Text-Based Posts Work on Social Media
- Brand Personality: 34% of consumers follow brands on social media to experience their personality, which is effectively communicated through text posts.
- Conversation Starters: Text posts can initiate discussions and help you understand your customers better, even in a landscape dominated by visual content.
Best Social Media Platforms for Text-Based Posts
| Platform | Advantages for Text-Based Posts |
|---|---|
| Ideal for engaging in Q&As and discussions with your audience. | |
| Best for sharing short, digestible updates, ideas, and news. | |
| Threads | A newer platform for text interactions and updates. |
| Perfect for professional content, thought leadership, and articles. |
User-Generated Content (UGC)

Source: Trend IO
UGC is created by your audience and repurposed by brands to showcase authentic experiences. It serves as social proof and can significantly broaden your reach.
Why User-Generated Content Works on Social Media
- Authenticity: UGC is perceived as the most trustworthy type of content because it reflects real customer experiences.
- Trust and Reach: 39% of consumers prefer seeing testimonials or demos from brands they follow, and 58% of consumers are influenced to choose a brand based on this type of content. UGC can also help extend your reach through followers of your followers.
- Cost-Efficiency: Utilizing UGC can be a budget-friendly strategy that leverages the content created by your customers.
Best Social Media Platforms for User-Generated Content
| Platform | Advantages for User-Generated Content |
|---|---|
| Highly effective for visual content and engaging with UGC through images and videos. | |
| TikTok | Ideal for video content, including short-form videos that showcase UGC. |
Audio
Source: Scape
Audio content, especially podcasts, offers an engaging way to connect with your audience through voice rather than visuals. This format allows for in-depth discussions and personal connections without requiring viewers to be on-screen.
Why Audio Content Works on Social Media
- Convenience: 32% of US users listen to podcasts while multitasking, such as driving.
- Genuine Connection: Audio allows for a personal touch, enhancing listener engagement.
Best Social Media Platforms for Audio
| Platform | Advantages for Audio Content |
|---|---|
| Spotify | Major platform for discovering and listening to podcasts. |
| Apple Podcasts | Widely used for podcast distribution and audience reach. |
| TikTok | Useful for sharing audio snippets or teasers to promote podcasts. |
| YouTube | Allows for sharing audio with visual elements to increase reach. |
How HerFirst100k Uses Audio Content
HerFirst100k enhances their podcast visibility by:
- TikTok Teasers: Short videos that promote their podcast and attract new listeners.
- YouTube Integration: Extending their reach by sharing podcast content on a platform with a large search engine presence.
URL/Links to Other Content
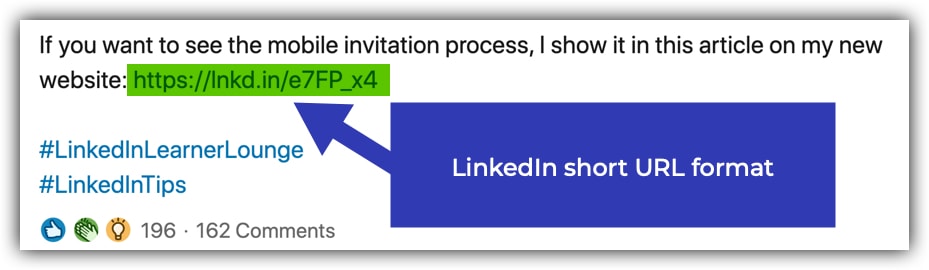
Source: John Espirian
Including URLs in your social media posts directs your audience to additional content, such as blog articles, product pages, or more detailed information on your website.
Why URL/Links Work on Social Media
- Traffic Generation: Links drive users to your website or specific content, potentially increasing engagement and sales.
- Ease of Access: Reduces friction in the user journey by providing direct access to further information.
Best Social Media Platforms for URL/Links
| Platform | Advantages for URL/Link Sharing |
|---|---|
| Ideal for professional content and business-related links. | |
| Allows for customized thumbnails and detailed descriptions. | |
| Convenient for short, direct links with thumbnail previews. | |
| Supports link previews and thumbnail images for better engagement. |
How Sprout Social Uses URL Content
Sprout Social effectively leverages URLs to:
- Feature Updates: Share new functionalities and integrations, driving engagement and potential sales.
- Social Media Articles: Direct users to their Insights blog, increasing traffic and visibility on industry topics.
Top Social Media Management Tools For Businesses
Social media marketing requires more than just posting content and hoping for engagement. It’s about maintaining an active presence, building a robust brand community, and managing your brand’s reputation. To streamline these processes, you need effective social media management tools that offer features such as post scheduling, performance analysis, team collaboration, and alert setting.
Here’s a roundup of some of the top social media management platforms to help you choose the best fit for your needs:
Sprout Social

Why Choose Sprout Social?
Sprout Social stands out as an all-in-one social media management tool that integrates seamlessly with major social networks, including Facebook, Instagram, TikTok, Twitter, LinkedIn, Pinterest, and YouTube. It allows you to manage your entire social media presence from a single dashboard, offering a comprehensive suite of tools to enhance your social media strategy.
Key Features:
- Social Media Publishing & Scheduling: Manage and schedule posts across multiple platforms from one interface.
- Monitoring & Analytics: Track your social media performance and analyze key metrics to refine your strategy.
- Smart Inbox: Consolidate incoming messages from different platforms into one easy-to-manage inbox.
- ViralPost: Automatically schedule your posts for times when your audience is most likely to engage.
- Hashtag Tracking: Identify popular and relevant hashtags to increase your content’s visibility.
- Custom URL Tracking: Gain insights into referral traffic and conversions generated by your social media posts.
- Employee Advocacy: Curate and share content through your employees’ networks to expand your brand’s reach and influence.
Additional Advantages:
- Integration with Reviews: Manage reviews from sources like Google My Business and Trustpilot.
- Shoppable Posts: Create posts that integrate with Facebook Shops and Shopify catalogs.
Best For: Comprehensive social media management and advanced analytics.
Zoho Social

Why Choose Zoho Social?
Zoho Social offers a robust set of features designed to manage every aspect of your social media presence. The platform excels in facilitating team collaboration and integrating with other Zoho products, making it a versatile choice for businesses looking for a collaborative and integrated approach to social media management.
Key Features:
- Customizable Scheduling: Schedule posts for optimal times tailored to each social network.
- Social Listening Dashboards: Track brand reviews, social mentions, and branded keywords to stay informed about your brand’s online presence.
- Integrated Inbox: Manage all customer interactions from a single location, avoiding the need to switch between multiple platforms.
- Team Collaboration: Collaborate with teammates via chat, audio, and video calls directly within the platform.
- CRM Integration: Instant integration with Zoho CRM for seamless monitoring of customer interactions and data.
Additional Advantages:
- Optimized Timing: Similar to Sprout Social, Zoho Social offers features for scheduling posts at the best times for engagement.
- Feedback and Reporting: Share reports and updates with your team to keep everyone aligned with your social media strategy.
Best For: Businesses needing a collaborative platform with CRM integration and advanced social listening capabilities.
HubSpot

Why Choose HubSpot?
HubSpot is a leading customer platform with powerful social media management features. Its centralized social inbox lets you keep track of all your social interactions in one place, providing contextual information through CRM integration. This insight allows you to enhance and personalize the customer experience effectively.
Key Features:
- Keyword Monitoring Streams: Identify important interactions and prioritize conversations that matter most to your brand.
- AI-Powered Social Media Post Generator: Simplify the publishing process with AI-driven tools that help create engaging content.
- Best Time to Post Suggestions: Optimize your scheduling with recommendations on the most effective times to post.
Additional Advantages:
- Organized Campaign Management: Tag marketing assets and content to associate posts with specific campaigns, making it easier to measure effectiveness.
- Comprehensive Tools: Includes essential features for publishing, scheduling, keyword monitoring, and social media reporting.
Best For: Integrated social media management with CRM capabilities and advanced AI tools.
Hootsuite

Why Choose Hootsuite?
Hootsuite is known for its robust scheduling and reporting features, making it a top choice for businesses managing multiple social media accounts and complex strategies. Its comprehensive analytics and team collaboration tools help streamline operations and track performance effectively.
Key Features:
- Multi-Platform Integration: Manage multiple social media accounts from a single dashboard.
- Post Scheduling: Schedule posts across various platforms and track engagement metrics.
- Analytics & Reporting: Generate detailed reports on social media performance and audience insights.
- Team Collaboration: Share tasks and manage team workflows effectively.
Benefits:
- Hootsuite’s robust scheduling and reporting features make it ideal for managing complex social media strategies.
Best For: Comprehensive management of multiple accounts with detailed analytics and team collaboration features.
Buffer

Why Choose Buffer?
Buffer is favored for its simplicity and user-friendly interface, making it a great choice for small to medium-sized businesses. It provides essential social media management features without overwhelming complexity, allowing teams to schedule posts, track performance, and collaborate effectively.
Key Features:
- User-Friendly Interface: Easy-to-navigate dashboard for scheduling posts and analyzing performance.
- Social Media Analytics: Monitor engagement, track performance metrics, and generate custom reports.
- Team Collaboration: Allow team members to collaborate on content creation and strategy.
Benefits:
- Buffer’s simplicity and ease of use make it a popular choice for small to medium-sized businesses.
Best For: Streamlined social media management with a focus on simplicity and ease of use.
Later

Why Choose Later?
Later stands out for its visual content calendar and focus on Instagram, making it ideal for businesses with a strong Instagram presence. Its tools for planning and scheduling visual content help streamline the process and enhance your Instagram strategy.
Key Features:
- Visual Content Calendar: Plan and schedule posts with a visual content calendar.
- Instagram Focus: Specializes in Instagram scheduling and content planning.
- Analytics: Track engagement metrics and optimize your Instagram strategy.
Benefits:
- Later’s focus on Instagram and visual content planning is perfect for businesses with a strong Instagram presence.
Best For: Businesses that prioritize Instagram and need a visual approach to content scheduling.
CoSchedule

Why Choose CoSchedule?
CoSchedule is ideal for businesses looking for a comprehensive content planning and automation solution. Its features for managing content across multiple platforms and automating social media posting help streamline marketing strategies and track performance effectively.
Key Features:
- Content Calendar: Plan and organize your content across multiple platforms.
- Automated Social Posting: Automate social media posting and repurposing of content.
- Marketing Analytics: Track performance and ROI of social media campaigns.
Benefits:
- CoSchedule’s content calendar and automation features are great for managing comprehensive marketing strategies.
Best For: Businesses looking for robust content planning and automation tools to enhance their marketing efforts.
Keyhole

Why Choose Keyhole?
Keyhole stands out for its influencer tracking and marketing capabilities, providing in-depth analytics to help you vet and compare influencers. Its detailed reporting helps measure the performance of influencers and their impact on your campaign goals.
Key Features:
- Automated Reports: Generate shareable and presentation-ready reports within seconds.
- Brand, Campaign, Hashtag, and Influencer Reporting: Detailed insights into various aspects of your social media performance.
Benefits:
- Keyhole’s focus on influencer tracking and performance measurement helps you optimize influencer campaigns and maximize ROI.
Best For: Businesses looking to track and evaluate influencer performance and enhance their influencer marketing strategies.
Sprinklr

Why Choose Sprinklr?
Sprinklr offers a comprehensive customer experience management platform with robust social media management features. Its UGC management capabilities, editorial calendar, and digital asset manager make it a powerful tool for amplifying brand reach and managing customer interactions.
Key Features:
- Sprinklr AI: Speed up content generation with AI-driven tools.
- Custom Approval Workflows: Streamline team collaboration and content approval processes.
- UGC Management: Organize and repost user-generated content to boost brand visibility.
- Customer Service Integration: Unified customer experience management through consumer intelligence integrations.
Benefits:
- Sprinklr’s focus on UGC and customer experience management makes it ideal for brands looking to enhance engagement and streamline their social media operations.
Best For: Businesses that need comprehensive customer experience management alongside social media management.
Social Media Trends You Need To Know
You don’t need to be a fortune teller to predict the social media trends set to dominate in 2024. A closer look at performance and consumer preference data provides a clear picture of the trends shaping the year ahead. Here’s a breakdown of key trends to watch and how they might influence your social media strategy.
Behind-the-scenes content
Why It’s Important: Today’s audience craves authenticity and transparency from brands. They want to see the inner workings of businesses and understand their values and practices. This shift towards transparency has become a vital component of building trust and credibility.
The Shift: While brands previously gained recognition by speaking out on social issues, the focus has now shifted towards demonstrating genuine transparency about business practices. Consumers are increasingly interested in areas such as labor practices, diversity, supply chain management, and environmental responsibility.
How to Leverage This Trend:
- Show Behind-the-Scenes Content: Share insights into your company’s daily operations, decision-making processes, and employee experiences to build trust and authenticity.
- Be Transparent: Regularly communicate your brand’s values, business practices, and social responsibility efforts to align with consumer expectations.
- Utilize Social Listening: Monitor conversations and trends to address any emerging issues proactively and adjust your transparency strategies as needed.
Key Takeaway: Transparency and authenticity are crucial in today’s social media landscape. By showcasing behind-the-scenes content and openly communicating your values, you can build stronger relationships with your audience and enhance your brand’s credibility.
Creating authentic content
Why It’s Important: Authentic content is increasingly resonating with audiences across all social media platforms. Non-promotional, genuine content from creators and employees tends to perform better and foster stronger connections with audiences.
The Shift: As creator culture continues to thrive, brands are recognizing the value of authentic, non-promotional content. Consumers are seeking genuine interactions and content that reflects real experiences rather than overt advertisements.
How to Leverage This Trend:
- Feature Authentic Voices: Collaborate with creators and employees to produce content that reflects real experiences and opinions.
- Avoid Over-Promotion: Focus on creating content that provides value and engages your audience without pushing overt sales pitches.
- Embrace User-Generated Content: Encourage and showcase content created by your audience to enhance authenticity and engagement.
Key Takeaway: Authenticity is key to resonating with today’s social media users. By prioritizing genuine content and featuring real voices, you can build more meaningful connections with your audience.
Posting playful content
 Why It’s Important: Gone are the days when an“edgy” brand voice dominated social media. In 2024, brands are shifting towards a more playful and relatable tone. This approach not only humanizes your brand but also helps you connect more authentically with your audience.
Why It’s Important: Gone are the days when an“edgy” brand voice dominated social media. In 2024, brands are shifting towards a more playful and relatable tone. This approach not only humanizes your brand but also helps you connect more authentically with your audience.
The Shift: Brands are increasingly tapping into meme culture and Internet trends to create content that resonates with a younger, more digitally savvy audience. This playful approach often involves light-hearted, humorous content that aligns with current trends and engages users in a fun and relatable way.
How to Leverage This Trend:
- Experiment with Content Formats: Incorporate memes, humorous posts, and playful visuals into your content strategy. Ensure that these elements align with your brand’s tone and values to maintain authenticity.
- Engage with Internet Culture: Stay updated with current trends and memes. Use these insights to create content that feels timely and relevant to your audience.
- Maintain Brand Consistency: Even as you embrace a playful tone, ensure that your content remains consistent with your brand’s overall image and message.
Key Takeaway: Playful content is becoming a key element of brand personality on social media. By integrating humor and relatability into your content strategy, you can create a more engaging and authentic connection with your audience.
The expansion of social commerce
Why It’s Important: Social commerce has evolved from a mere trend into a significant component of online shopping. The integration of shopping features within social media platforms allows users to make purchases directly from their feeds, combining entertainment with convenience.
The Shift: Platforms like TikTok are leading the charge in social commerce. The official launch of TikTok Shop in the US in late 2023, along with ongoing efforts to streamline in-app shopping, highlights the growing importance of social commerce. Live streaming and interactive shopping experiences are also gaining traction, offering brands new ways to connect with consumers.
How to Leverage This Trend:
- Integrate Social Commerce Features: Utilize in-app shopping features on platforms like TikTok and Instagram to provide a seamless shopping experience for your audience.
- Host Live Shopping Events: Consider hosting live shopping events that combine product demonstrations with interactive features. These events can enhance engagement and drive sales.
- Track and Analyze Performance: Monitor the effectiveness of your social commerce efforts through analytics and adjust your strategy based on performance data.
Key Takeaway: Social commerce continues to expand, offering new opportunities for brands to engage with consumers and drive sales directly through social media platforms. Embrace this trend by integrating shopping features and interactive experiences into your strategy.
Leveraging social media data
Why It’s Important: Social media data is not just a tool for marketing teams; it has far-reaching implications that can benefit various departments across an organization. Leveraging social media insights can drive improvements in product development, customer support, public relations, and overall business strategy.
The Shift: Historically, social media data was primarily used by marketing teams to gauge campaign performance and audience engagement. However, a growing recognition of its broader value is reshaping how organizations utilize this data. According to recent data, 76% of marketers agree that social media insights are instrumental for informing other departments. This indicates a shift towards a more integrated approach where social data informs and enhances various aspects of the business.
How to Leverage This Trend:
- Integrate Social Data Across Departments: Ensure that social media insights are shared with teams beyond marketing. For instance, customer support teams can use social data to understand common customer issues, while product teams can use it to gather feedback on product features.
- Use Data to Drive Product Development: Analyze social media conversations to identify emerging trends, customer preferences, and potential areas for product improvement. This can help in developing products that better meet customer needs and expectations.
- Enhance Customer Support: Monitor social media channels for customer feedback and complaints. Use this data to address issues more effectively and improve overall customer satisfaction.
- Inform PR and Communications Strategies: Utilize social media insights to shape your public relations strategies and messaging. Understanding what resonates with your audience can help craft more compelling and relevant communication.
Key Takeaway: Social media data is a valuable resource that extends beyond marketing. By integrating these insights across various departments, organizations can enhance their product offerings, improve customer support, and refine their PR strategies, leading to a more cohesive and informed business approach.
SEO not just for websites but also for social media platforms
Why It’s Important: Social media platforms are increasingly becoming key players in the search landscape. As more users, especially younger generations, turn to social media for information, optimizing your content for discoverability on these platforms is essential.
The Shift: In recent years, social media has evolved from being merely a platform for engagement to a powerful search tool. For instance, nearly 40% of Gen Z users preferred TikTok over Google for searching information in 2022. This shift underscores the growing importance of optimizing your social media content to enhance visibility and reach.
How to Leverage This Trend:
- Optimize Your Content: Use relevant keywords, hashtags, and geo-tags to improve the discoverability of your posts on platforms like Instagram, TikTok, and Pinterest.
- Engage with Trending Topics: Stay updated with current trends and incorporate them into your content strategy to increase your visibility in social searches.
- Monitor Search Trends: Utilize social media analytics tools to track search trends and adjust your strategy accordingly.
Key Takeaway: Social media is becoming a significant search engine, making SEO optimization for social channels as crucial as it is for your website. Enhancing the discoverability of your content on these platforms can significantly boost your reach and engagement.
Frequently Asked Questions
What is social media content marketing?
Social media content marketing involves creating and sharing content on social media platforms to achieve marketing and branding goals. This includes engaging posts, videos, and other media to connect with target audiences.
Why is social media content marketing important for businesses in Singapore?
In Singapore, social media is a key platform for reaching a tech-savvy and engaged audience. Effective content marketing helps businesses build brand awareness, drive traffic, and foster customer loyalty in a competitive market.
How often should businesses post content on social media?
The ideal posting frequency depends on the platform and your audience. Generally, posting consistently is key. For instance, businesses might post daily or several times a week on platforms like Instagram and Facebook, while LinkedIn posts may be less frequent, such as once or twice a week. Regular posting keeps your brand top-of-mind and helps maintain engagement.
How can businesses measure the success of their social media content marketing efforts?
Success can be measured using key performance indicators (KPIs) such as engagement rates (likes, comments, shares), reach and impressions, click-through rates, conversion rates, and overall growth in followers. Tools like Google Analytics, platform-specific insights, and social media management tools can help track these metrics and assess the effectiveness of your strategies.
What types of content perform best on social media platforms in Singapore?
In Singapore, content that tends to perform well includes visually engaging posts, informative videos, and interactive content such as polls and quizzes. Content that highlights local events, trends, or cultural references also resonates well. Additionally, user-generated content and behind-the-scenes looks can foster a stronger connection with the audience.